AFFORDABLE, EASY & POWERED BY AI
Lease Management Software
to Track Your
Leasecake’s user-friendly, lease management software alerts you to critical dates, keeps lease and location documents all in one place, and provides financial oversight, so you can focus on what really matters: growing your business.
AFFORDABLE, EASY & POWERED BY AI
Lease Management Software
to Track Your
Leasecake’s user-friendly, lease management software alerts you to critical dates, keeps lease and location documents all in one place, and provides financial oversight, so you can focus on what really matters: growing your business.
Today's Top Brands Rely on Leasecake For Lease Management Software










The easiest lease management software you'll ever use
Leverage our leasing management software in one easy-to-use platform to solve multiple lease administration headaches. Minimize location risks, drive lease negotiation, and access comprehensive, accurate data for your entire real estate portfolio.
Leases
Assets
Dashboards
Accounting
Contracts
Tasks
Reporting
Permits & Licenses
Collaboration
INTRODUCING CAKEBOT
Supporting the future of fast, affordable lease management
Unlock the Power of AI with Our Lease Management Software: Streamline document understanding, empower your teams, and transform complex language into actionable insights.
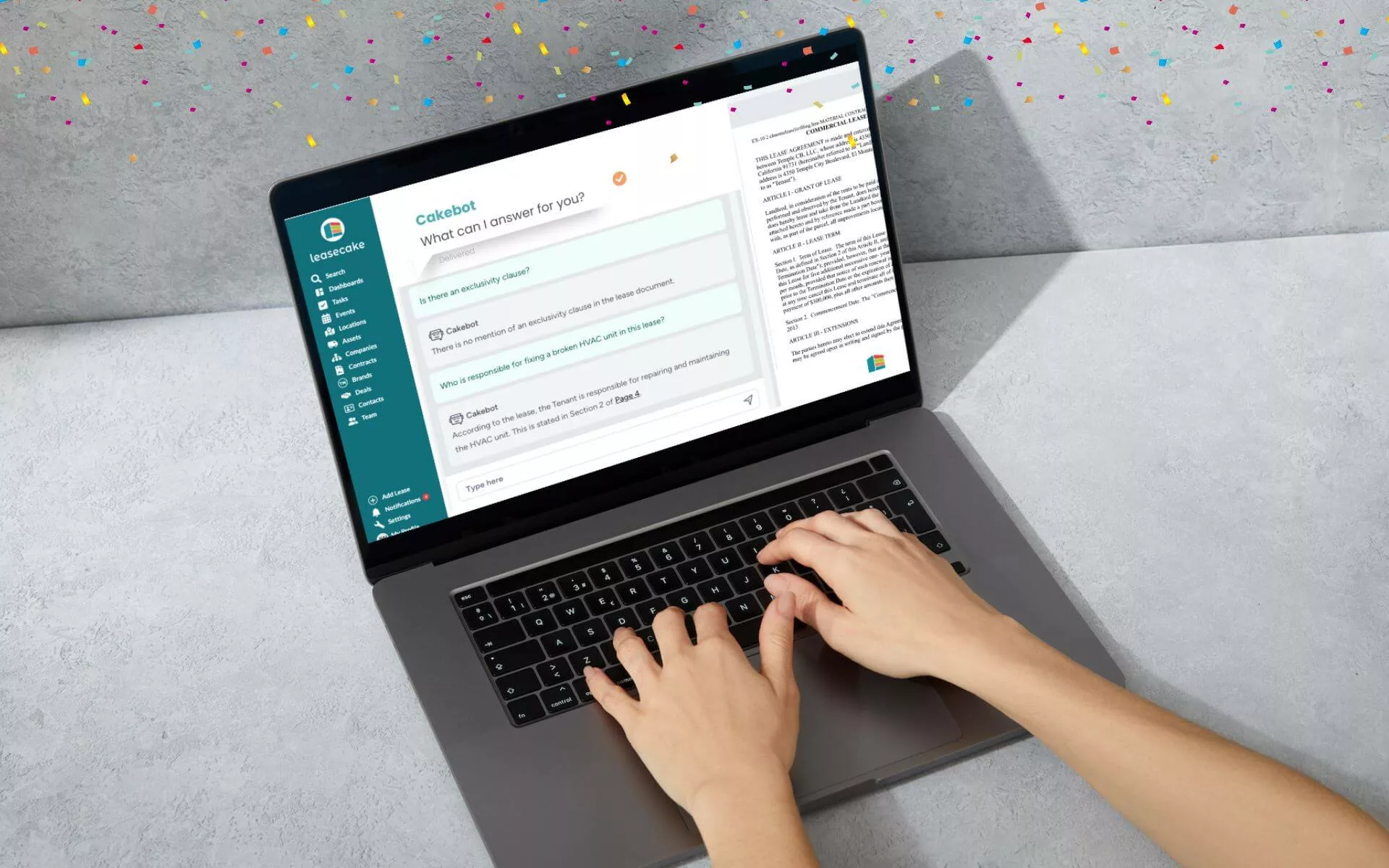
Easy
Lease understanding made easy for everyone.
24/7
Your virtual real estate expert, available round-the-clock.
Fast
Get the support you need at a pace that keeps up with the market.
PROFESSIONAL SERVICES
Real Estate Experts
to Help You Grow
Our team of real estate experts make abstraction a breeze by reviewing and extracting key information from your leases for full transparency.
Our platform tracks payments and generates reports to demonstrate compliance with lease accounting standards ASC 842 and IFRS 16 so you’re ready for your next audit.
We’ll ensure you’re paying your fair share of expenses as dictated by the terms and conditions of the lease—nothing more.
Our audit services help you identify areas to optimize or improve your leases, and to better prepare you for successful negotiations.




OUR CUSTOMERS
The perfect recipe for restaurant and retail growth
Food & Beverage
Service & Retail
Discover how we're backing the rapid expansion of gyms, salons, medtail & more

Which Wich Franchisee, 17+ Locations
"Leasecake reminders eliminate the worry of missing a critical date. It is the perfect tool for organizing multiple leases and never missing a renewal date or rate increase notice."

Sola Salons, 595+ Locations
"I chose Leasecake because it's the only product that is really designed for tenants and franchisees. It's easy to use and helps us keep track of leases without spreadsheets."

Smile Partners USA, 89+ Locations
"Leasecake has made our lives easier. The time saved with the ASC842 calculation is massive, I would estimate over 100 hours desk time saved over the past 18 months."
CASE STUDY
Domino's Franchisee
As the controller for Team WOW, Tim Doktorski was on the lookout for a software product that would help him get better control of all the information surrounding the 69 Domino’s Pizza properties in his portfolio.

